How London-Based MindLink Is Transforming Real-Time Classified Communication?
In the spring of 2021, the UK’s Carrier Strike Group 21 set sail on a 28-week global deployment headed by HMS Queen Elizabeth, the most powerful British warship ever built. The mission took the strike group through contested waters. The security of every operational communication between commanders, coalition partners, and allied intelligence assets was not a background concern. It was the central operational requirement on which the mission’s success depended. Providing the secure collaboration infrastructure that kept those communications flowing continuously, including the real-time provision of locational data on allied and hostile forces and the delivery of strategic Indicators and Warnings to the strike group throughout the deployment, was MindLink.
That a London-based software company founded in 2011 by a small team focused on financial trading chat was, by 2021, the trusted secure communication backbone of a NATO carrier strike group in active deployment is not an accident of timing. It is the product of a decade of deliberate, exacting engineering conducted in close partnership with the most demanding security customers in the world.
From Trading Floors to Top-Secret Environments: The MindLink Origin Story
MindLink was established in 2011 as a chat software company serving financial institutions. The problem it was solving at the time was recognisably commercial: trading partners in fast-paced markets needed to collaborate in real time, with reliability and with sufficient structure that the information exchanged could be tracked, governed, and audited. The platform worked. Its ability to deliver what the company describes as a provable decision advantage, the capacity to make faster, better-informed decisions because information flows more reliably, attracted the attention of a customer profile that had not been part of the original plan.
The UK and US intelligence community identified in MindLink a collaboration architecture that could solve a much harder version of the same problem. Where financial trading rooms needed fast and governed information sharing, intelligence operations needed fast, governed, and classified information sharing, at the highest possible security levels, across organisational and national boundaries, in environments where the consequences of data spillage were not measured in money but in operational security and human lives.
By working in close partnership with the intelligence community for nearly a decade, MindLink re-engineered its platform from its commercial foundations into a purpose-built secure mission collaboration system following a zero-trust architecture and a data-centric security model. The result is a platform that today holds the Authority to Operate across multiple deployments in significant member organisations of the Global Intelligence Community, is registered in both the US and UK with the relevant procurement and defence supply chain systems including CAGE, SAM, PIEE, and NCAGE, and operates from offices in London’s Borough High Street and Los Angeles.
The product it has built is not a consumer messaging app with extra encryption bolted on. It is a specialist system designed from the ground up for environments where no commercial off-the-shelf product is adequate, and where the cost of failure is not recoverable.

Zero-Trust by Architecture: The Four Security Pillars of the MindLink Platform
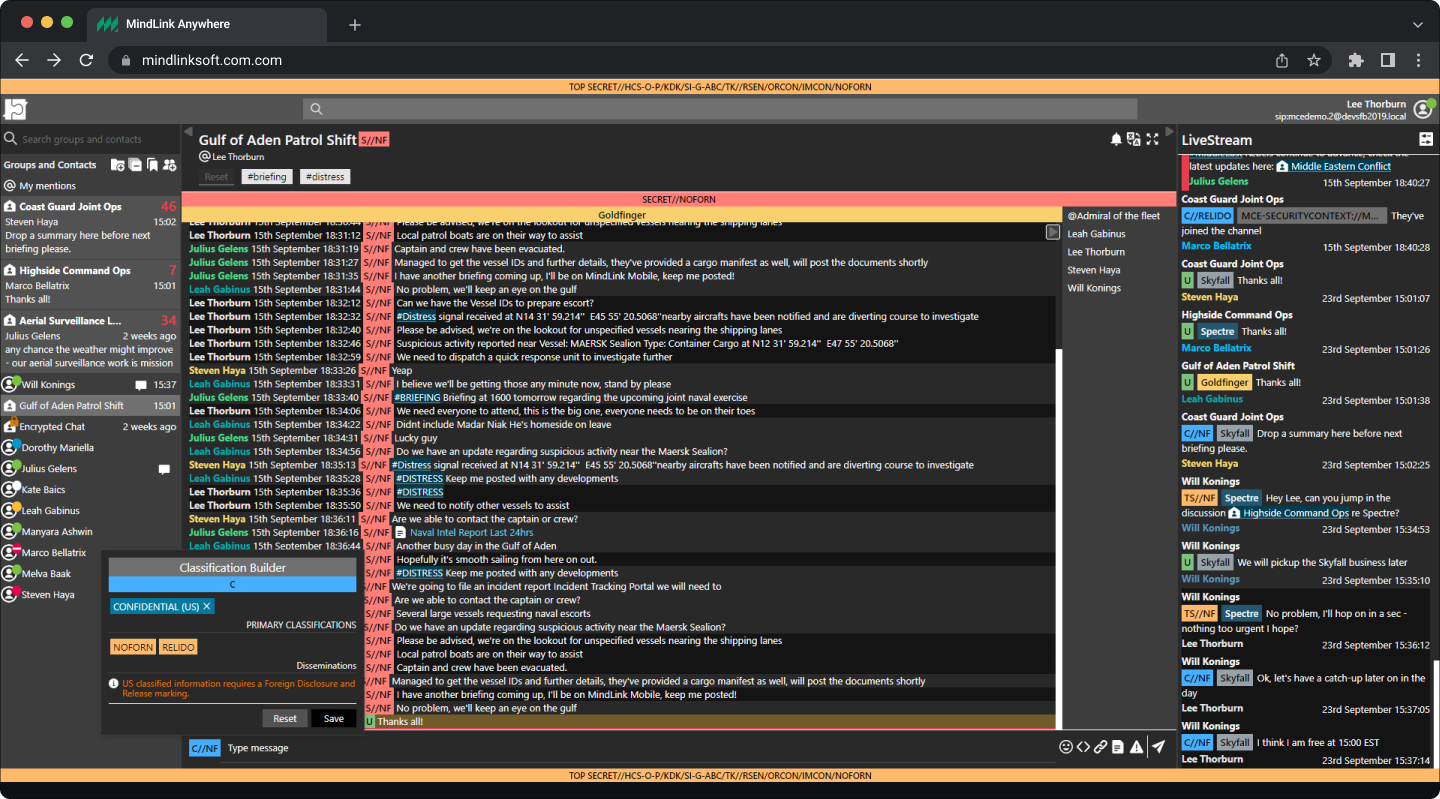
The MindLink platform’s security model is organised around four interconnected principles, each derived from practices developed by and for the intelligence community rather than adapted from commercial security frameworks. Together, they constitute what MindLink describes as data-centric security: a model in which security is embedded in the data itself rather than enforced only at the network perimeter.
This distinction is critical in environments where the perimeter is not a fixed boundary but a dynamic coalition of organisations with different clearance levels, different access rights, and different information-handling requirements operating simultaneously.
- Attribute-Based Access Control (ABAC): MindLink’s security engine governs access through secret attributes, roles, and security clearances sourced from trusted third-party identity directories. Chat room access rights are configured at multiple levels of privilege and granularity using expressive, role-based permissioning rules. This enables information to flow across the mission theatre while ensuring that governance and confidentiality of sensitive data is maintained at every point.
- Sub-Compartment Security Model: MindLink’s architecture is rooted in the “Communities of Interest” paradigm advocated by the intelligence community. All system components, including chat rooms, users, and content, are segregated into secure compartments that enforce strong access-control boundaries, define explicit data handling procedures, and mitigate spillage risks. Sensitive information reaches only those with a verifiable, current need to know.
- Information Assurance: MindLink protects sensitive information using techniques developed specifically for TOP SECRET handling by the intelligence community. These mechanisms, which combine technology, policy, and human behaviour guidance, are provided natively within the platform as first-class safeguards. No external components are required, eliminating integration points that would introduce attack surface or single points of failure.
- Enterprise End-to-End Encryption (EE2EE): MindLink’s end-to-end encryption uses an innovative zero-trust approach built on Communities of Interest. Independent key sharing and key protection systems enable end-to-end encryption at room scale without the complex peer-to-peer trust requirements that make encryption impractical at mission scale. This directly mitigates insider threat, the largest attack surface in a typical chat system, without limiting participation or performance.
The platform also supports native data classification labelling across client sessions, conversations, and individual messages in formats that are both machine-readable and human-readable. This dual readability is significant: machine-readable classification enables automatic access control based on a user’s security attributes without requiring human intervention at every permission decision, while human-readable classification ensures that users are always aware of what they are handling and with whom it can be shared. The risk of inadvertent data spillage, one of the most persistent and consequential vulnerabilities in classified environments, is structurally reduced rather than merely warned against.
Operating Where Commercial Platforms Cannot: DDIL Environments and Air-Gapped Deployments
The environments in which MindLink operates extend significantly beyond the conditions under which commercial collaboration platforms are designed to function. The platform is built to operate in Denied, Disrupted, Intermittent, and Limited bandwidth environments, referred to in the defence community as DDIL conditions. A carrier strike group at sea, a forward operating base in a remote theatre, a coalition command post in a region where communications infrastructure is unreliable or actively contested: these are environments where a platform that requires stable, high-bandwidth internet connectivity is simply not deployable. MindLink’s architecture is designed to function under variable communications conditions, maintaining mission collaboration capability even when connectivity is degraded or intermittent.
The platform is additionally deployed in air-gapped environments, systems that are physically isolated from public networks and from each other, at the highest classification levels. Deploying a real-time collaboration platform in an air-gapped environment requires solving a set of technical problems that commercial vendors rarely confront: how do users authenticate without access to cloud-based identity providers? How do encryption keys get exchanged without internet connectivity? How does the platform maintain consistent performance when it cannot rely on cloud infrastructure for processing or storage?
MindLink’s on-premise deployment model, zero external dependencies for core security functions, and ABAC integration with locally deployed Identity and Access Management systems address each of these problems directly.

The FRNIX Federation Protocol: Secure Information Sharing Across Coalition Boundaries
One of the defining operational challenges of modern national security is that missions are rarely executed by a single organisation. NATO operations involve dozens of member nations. Intelligence sharing under the Five Eyes framework, spanning the UK, United States, Canada, Australia, and New Zealand, requires information to cross national and organisational boundaries in real time while remaining subject to the classification and access controls of each contributing organisation.
Standard enterprise federation protocols are not designed for this requirement: they handle identity and authentication across organisational boundaries, but they do not handle classification, entitlements, encryption key exchange, and data leakage prevention simultaneously. MindLink’s FRNIX federation protocol was built specifically to address all four.
FRNIX Federation Protocol is Designed for exceptionally classified coalition operations. Four problems, one protocol.
- Classification: Sensitivity and dissemination controls for classified materials are preserved across organisational boundaries. A message classified at a given level retains that classification when it crosses into a partner organisation’s domain.
- Entitlements: Federated identity is authorised and validated across organisations. Users are authenticated against their home organisation’s identity systems while their access rights in the partner environment reflect their actual clearances.
- Encryption: Encryption keys are shared across federated organisations using the Communities of Interest model, enabling end-to-end encryption without the complex peer-to-peer trust establishment that makes cross-organisation encryption impractical at scale.
- Data Leakage Prevention: Specific sensitive information is prevented from leaving an organisation regardless of what users request or what system errors occur. DLP is enforced at the protocol level, not only at the application level.
MindLink also provides deep ethical walling within federated environments, a multi-layered access control system based on intelligence community best practices for managing secret attributes, roles, and clearances across coalition partners. The FRNIX protocol additionally follows a highly efficient network architecture specifically designed for remote and forward deployed scenarios, maintaining federation capability under the DDIL bandwidth conditions that coalition operations frequently encounter.
A coalition partner operating from a forward position with limited satellite bandwidth can remain a participant in the federated intelligence network without requiring the stable, high-capacity connection that commercial federation solutions assume.

The XMPP Gateway, API Integration, and the Mission Application Ecosystem
MindLink’s product suite extends beyond its core collaboration platform to address the integration requirements that mission environments impose. Two products are particularly significant in this context: the XMPP Federation Gateway and the MindLink API.
The XMPP Federation Gateway enables interoperability between MindLink deployments and other XMPP-based communication systems that defence and intelligence organisations may already have deployed. XMPP, the Extensible Messaging and Presence Protocol, is an open standard for real-time communication that has been adopted by numerous government and defence collaboration systems.
The MindLink XMPP gateway allows these existing systems to participate in MindLink-federated networks without requiring wholesale platform replacement, protecting prior technology investments while extending the security and classification capabilities of the MindLink platform to existing infrastructure. Organisations that have invested in XMPP-based systems over years can bring those investments inside the MindLink security perimeter rather than choosing between them.
- Instant Messaging: One-to-one, direct, private conversations with full classification labelling and access control at the message level.
- Persistent Group Chat: Many-to-many discussions with observable, searchable message history. Secure compartment boundaries enforced across all participants.
- Mission Application Integration: API connectivity enabling automated mission information sharing from ISR feeds, sensor systems, and mission management applications directly into classified chat environments.
The MindLink API enables mission applications, intelligence feeds, sensor systems, and automated data sources to push information into the MindLink collaboration environment programmatically. In practice, this means that a signals intelligence feed, an imagery analysis output, a geospatial tracking system, or a mission management application can deliver its data directly into classified chat channels where the relevant analysts and commanders are working, without requiring those users to monitor separate systems or manually move information between environments. The integration of automated mission information sharing into the collaboration platform closes a critical operational gap: the gap between where information is generated and where decisions are made.

Authority to Operate, FVEY Deployment, and MindLink’s Position in the Global Security Architecture
The validation that matters most in MindLink’s market is not a certification checklist. It is the Authority to Operate, the formal approval issued by a government security authority that a platform meets the requirements to process classified information in a specific environment. MindLink holds ATO across multiple deployments in significant member organisations of the Global Intelligence Community, including within FVEY, the intelligence alliance comprising the United Kingdom, United States, Canada, Australia, and New Zealand that represents the world’s most sophisticated and deeply integrated intelligence sharing network.
Operating at scale inside FVEY is not a credential that a platform acquires through a procurement process. It is the outcome of sustained technical partnership, continuous security evaluation, and a demonstrated ability to meet requirements that most commercial software was never designed to approach.
“MindLink Chat Engine enables our internal users and external coalition partners to collaborate effectively and securely in active mission scenarios. By enforcing data classification and end-to-end encryption we minimise the risk of data spillage to better protect the mission. MindLink not only increases our data security posture but directly impacts our ability to make critical decisions in real-time and brings focus to mission execution.” US Government, Technology Consultant
MindLink’s vision is explicit: to be the leading specialist in mission-critical collaboration systems and to deploy its products as the global backbone for mission operations. That ambition is stated with the confidence of a company that has already been stress-tested against the most demanding operational requirements its market produces. It has operated during a carrier strike group’s maiden voyage through contested waters. It has been evaluated and approved by the intelligence agencies of multiple FVEY nations. It has been deployed in air-gapped environments at the highest classification levels and in DDIL conditions at the forward edge of coalition operations.
The question for a platform with those credentials is not whether it has proven its technology. The question is the scope and pace at which that technology can be deployed across the full breadth of a defence and intelligence community that is increasingly recognising that the speed and security of information sharing are not competing requirements but the same requirement expressed from different angles. For MindLink, the mission and the market are the same thing.